Watch Out for Tech Support Scams
Authored By: Genisys Credit Union on 9/27/2017  It's easy for anyone that has never been taken for a ride by a con artist to wonder how people can fall for such scams.
It's easy for anyone that has never been taken for a ride by a con artist to wonder how people can fall for such scams.
Yet according to the Federal Trade Commission, two out of three people have experienced a tech support scam in the previous 12 months. And more than $24.6 million has been lost to tech-support scams alone in the last two years.
While these scams are very sophisticated, learn how easy it is to avoid falling victim to these scams.
Cybercriminals use a variety of tactics to defraud consumers from cold-calling and web advertising to persistent and annoying pop-up windows. The global network behind these fraudsters includes people who would sell your consumer information to generate leads, call center operations across the world that are trained to convince you they you a non-existent technical problem, and software developers who create fake tools that could be installed on your computer or other device.
Here are the most common tech support scams and what you should do if it happens to you:
Telephone tech support scams:
In this scam, fraudsters call you and claim to be from Microsoft or Apple Tech Support. They offer to help solve your computer problems. Once they've gained your trust, they might ask for your username and password or ask you to go to a legitimate website to install software that will let them access your computer to fix it. Once you do this, your computer and your personal information are vulnerable.
Fraudsters often use publicly available phone directories, so they might know your name and other personal information when they call you. They might even guess what operating system you're using.
REMEMBER: Microsoft and Apple do not make unsolicited phone calls.
If you receive an unsolicited call from someone claiming to be from Microsoft or Apple Tech Support, hang up. They DO NOT make these kinds of calls.
Scam Pop-Ups:
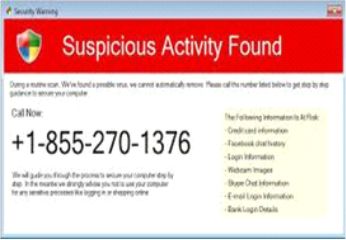
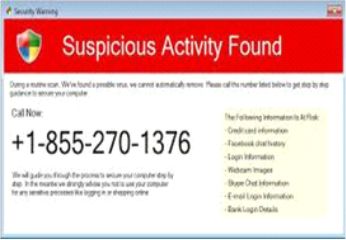
Another trick is the website pop-up – you know, that little browser window that sometimes appears while you’re searching the Web. Fraudsters set up websites with scam pop-ups that have an alarming message and phone number to call for help.
These pop-ups usually are not easy to close and are traps that attempt to mislead you into revealing sensitive personal or financial information. They could also prompt you to pay for fake anti-virus software or even install malware and viruses onto your device.
Do not call the number in the pop-up. Microsoft and Apple’s error and warning messages never include a phone number.

How the Scam Works
Scammers may call, place alarming pop-up messages on your computer, offer free “security” scans, or set up fake websites – all to convince you that your computer is infected. The scammers try to get you on the phone, and then work to convince you there’s a problem. Finally, they ask you to pay them to fix that non-existent problem.
To convince you that both the scammers and the problems are real, the scammers may:
- pretend to be from a well-known company – like Microsoft or Apple
- use lots of technical terms
- ask you to get on your computer and open some files – and then tell you those files show a problem (when they don’t)
Scammers even have the ability to turn a computer screen dark, make the images look fuzzy and convince a consumer there is a problem.
Once the scammer has convinced you that your computer has a problem, they might:
- ask you to give them remote access to your computers, which lets them change your computer settings and makes your computer vulnerable to attack
- trick you into installing malware that gives them access to your computer and sensitive data like usernames and passwords
- try to sell you software that’s worthless, or that you could get elsewhere for free
- try to enroll you in a worthless computer maintenance or warranty program
- ask for credit card information so they can bill you for phony services or services you could get elsewhere for free
- direct you to websites and ask you to enter your credit card number and other personal information
These scammers want to get your money, access to your computer, or both. But there are things you can do to stop them.
If You Get a Call or Pop-Up
- If you get an unexpected or urgent call from someone who claims to be tech support, hang up. It’s not a real call. And don’t rely on caller ID to prove who a caller is. Criminals can make caller ID seem like they’re calling from a legitimate company or a local number.
- If you get a pop-up message that tells you to call tech support, ignore it. There are legitimate pop-ups from your security software to do things like update your operating system. But do not call a number that pops up on your screen in a warning about a computer problem.
- If you’re concerned about your computer, call your security software company directly. Don’t use the phone number in the pop-up or on caller ID. Instead, look for the company’s contact information online, or on a software package or receipt.
- Never share passwords or give control of your computer to anyone who contacts you.
Your best bet to avoid being caught in a scam is to never click on links in suspicious emails. If you get a pop-up message that tells you to call tech support, ignore it. Do not call a number provided on your screen via a pop-up that warns of a computer problem.
If you paid for bogus services with a credit card, call your credit card company and ask to reverse the charges. Check your statements for any charges you didn’t make, and ask to reverse those, too. Report it to ftc.gov/complaint.
© Genisys Credit Union and www.genisyscu.org, 2017. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Genisys Credit Union and www.genisyscu.org with appropriate and specific direction to the original content.
https://www.usatoday.com/story/money/business/2017/05/21/tompor-ftc-declares-war-tech-support-scams/101953542/
https://www.consumer.ftc.gov/articles/0346-tech-support-scams
« Return to "Blog"

 It's easy for anyone that has never been taken for a ride by a con artist to wonder how people can fall for such scams.
It's easy for anyone that has never been taken for a ride by a con artist to wonder how people can fall for such scams.